Another misleading title, but it is fun to write it down so why not?
In this post (8 pictures long) we have two parts:
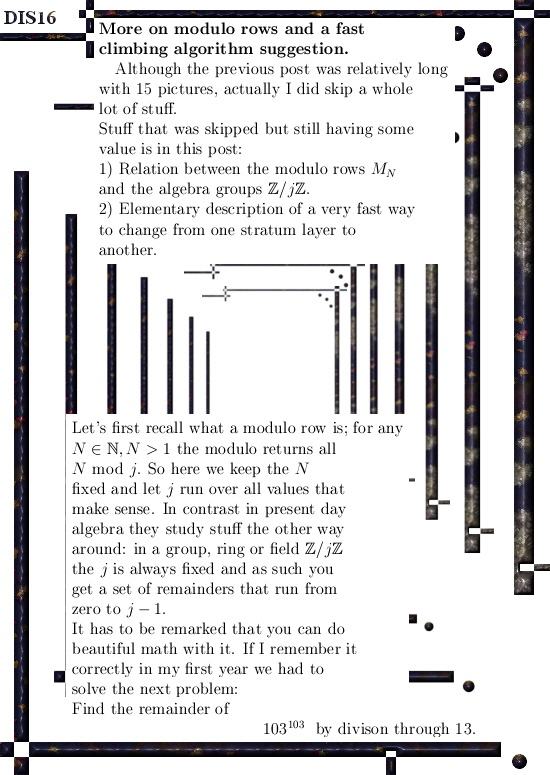
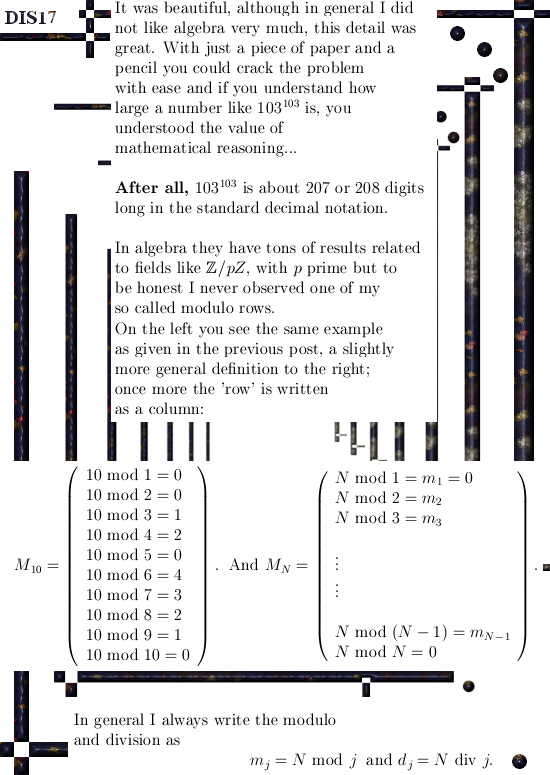
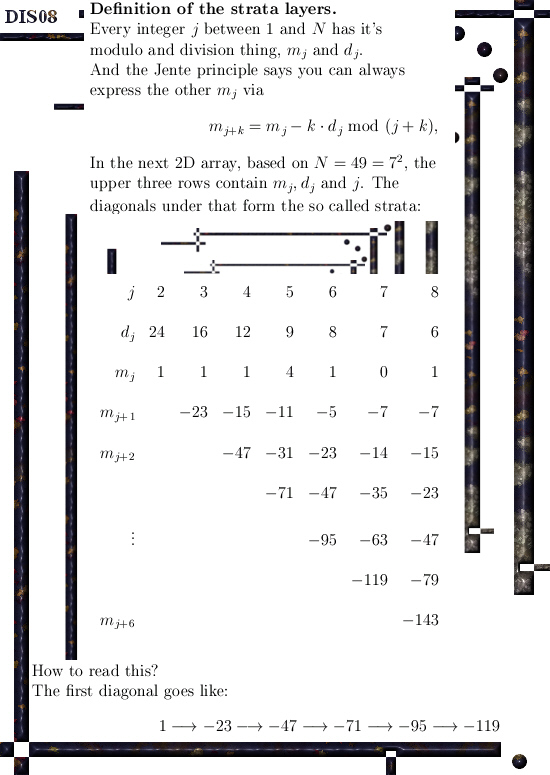
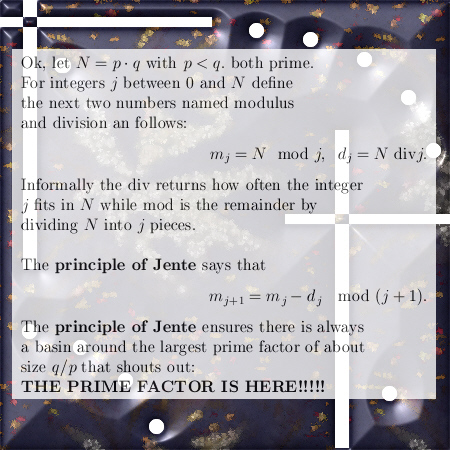
Part 1: The relation between the modulo row’s and the modular arithmetic groups Z/jZ.
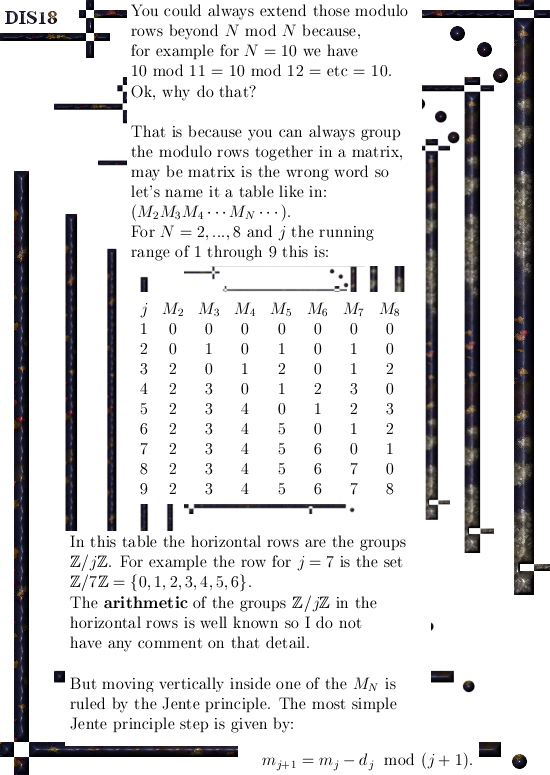
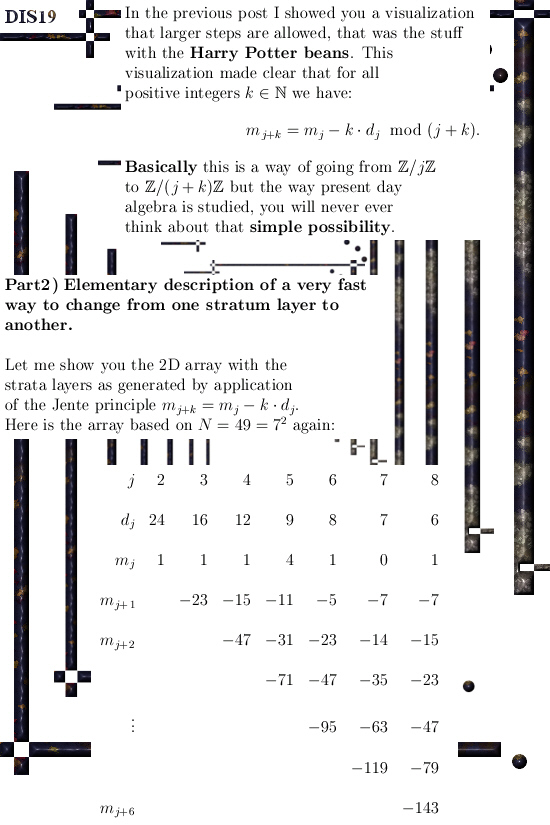
Part 2: A proposal (or schematic outline) of an important part of the algorithm that brings you from one stratum to the other.
I think this is my last post on this subject of modulo row’s.
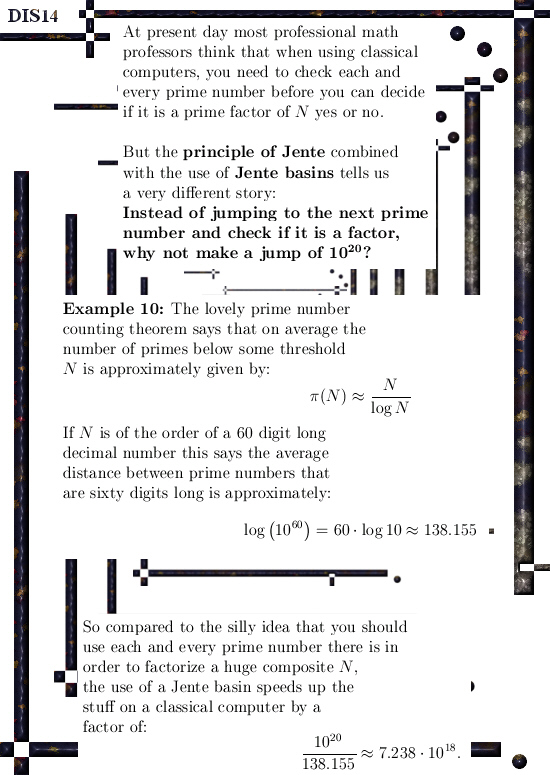
Lately websites using RSA encryption methods (that is why we look at large prime numbers made of two factors N = p*q) have gone from a 1048 bit long key to 2096 binary digits long keys. The idea is that it makes life just so much more safe; but the important part of the algorithm for transport over the strata is remarkable resilient towards such moves…
Furthermore, doubling the length of the encryption keys (squaring the size so to say) will in general also increase the size of the Jente basin as found just before the largest prime factor q.
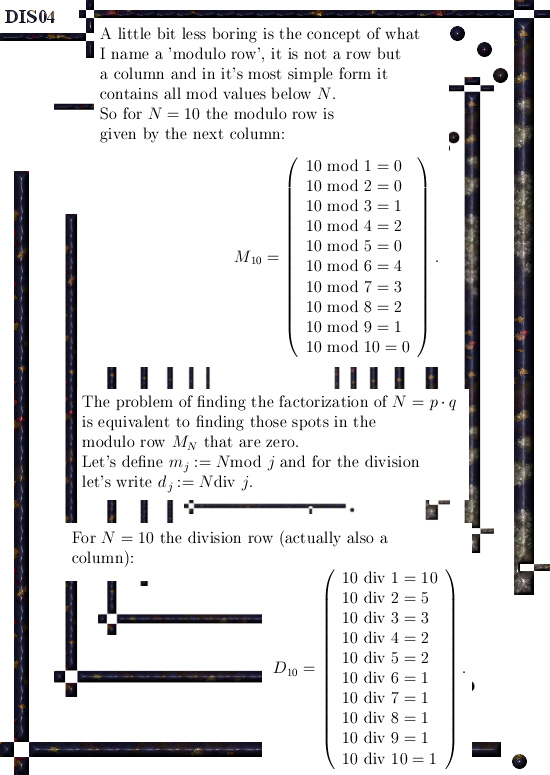
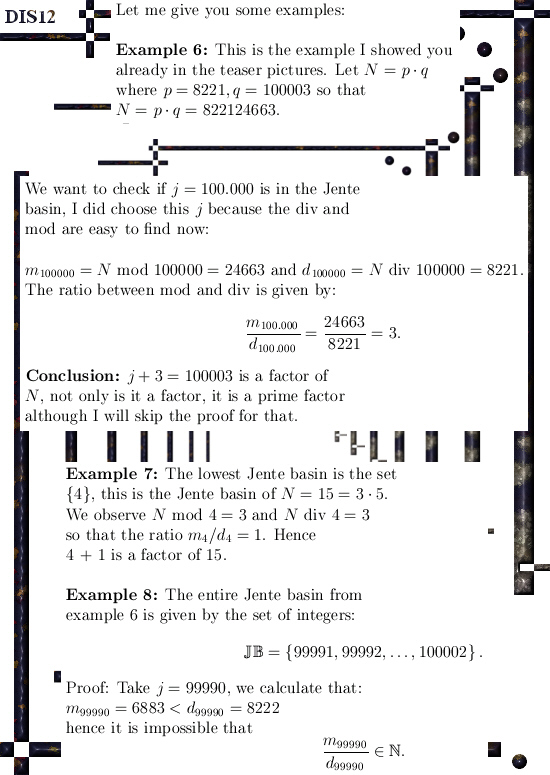
I do not claim to know a lot about encryption, but as far as I know there is zero point zero use of idea’s like the Jente basin. People use a lot of so called ‘trial division’ but even that is not a real division but mostly just taking N modulo something.
For example; want to know if the number 73 is a factor of N?
They simply calculate N mod 73 and if the outcome is 0 they say that 73 is a factor of N, otherwise it is not. The use of idea’s like a Jente basin so you can scrap a lot of trial numbers in the region you are in is, as far as I know, not used.
To be honest, I also do not know how they factor large hundreds of decimal digits long numbers anyway; so it might very well be they use similar idea’s. But if that were the case why is everybody else only talking about taking a huge number of trial divisions without any strategy behind that?
The numbering of the pictures is a continuation of the previous post.
Here are the 8 pictures, have fun reading it.
At this point in time the so called quantum computers are going from the lab to the field, anyway a lot of people claim this. But since after my humble opinion electrons have one electric charge and one of two possible magnetic charges, it will be a long long time before we have a working quantum computer based on electron spin.
Just like IBM with their racetrack technology for 3D memory; the idea is ok but at IBM too they think electron spin a like a vector and not like a charge. And voila; year in year out you never hear from it again…
Ok, for the time being this is what I had to say. See you in the next post.